- EvilProxy is a reverse-proxy service platform that promises to steal authentication tokens to defeat multi-factor authentication on many sites. The service allows low-skill threat actors who don’t know how to set up reverse proxies to steal otherwise well-protected internet accounts.
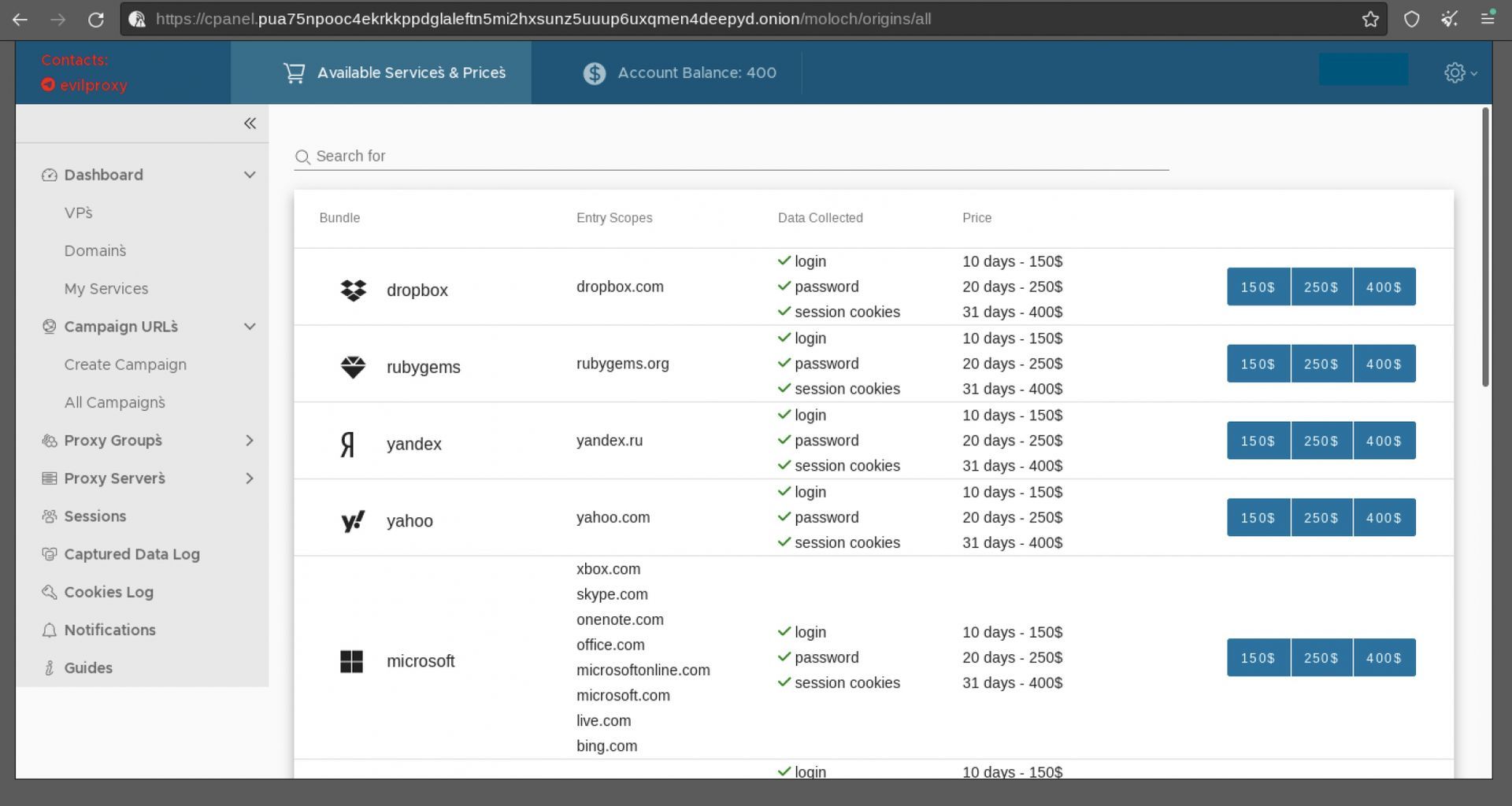
- The business claims to steal usernames, passwords, and session cookies for $150 for ten days, $250 for twenty days, or $400 for a month-long campaign.
- Attacks against Google accounts are more expensive, costing $250/450/600.
- Services like EvilProxy effectively bridge the skill gap and provide low-tier threat actors with a low-cost option to steal important accounts.
EvilProxy is a reverse-proxy Phishing-as-a-Service (PaaS) platform that promises to steal authentication tokens to defeat multi-factor authentication (MFA) on Apple, Google, Facebook, Microsoft, Twitter, GitHub, GoDaddy, and even PyPI. The service allows low-skill threat actors who don’t know how to set up reverse proxies to steal otherwise well-protected internet accounts.
What is reverse proxy phishing?
Servers between the intended victim and a genuine authentication endpoint, such as a company’s login form, are reverse proxies. When a victim visits a phishing page, the reverse proxy shows the legal login form, passes requests to the company’s website, and returns answers.
When a victim inputs their credentials and MFA on the phishing page, they are sent to the genuine platform’s server, where the user is logged in and a session cookie is returned.
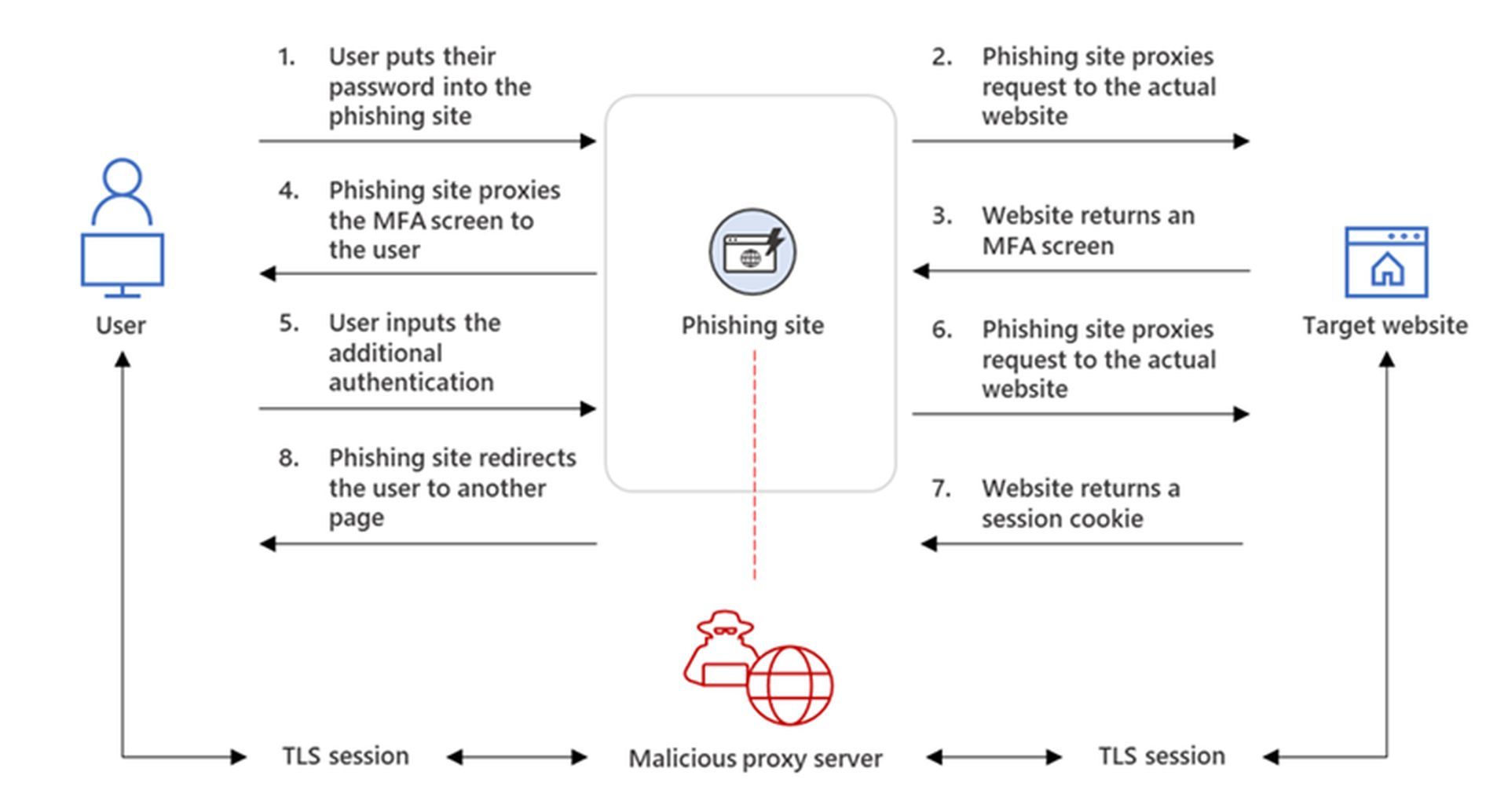
However, because the threat actor’s proxy is in the middle, it can take the authentication token from the session cookie. Threat actors can then utilize this authentication cookie to log in to the site as the user, circumventing any multi-factor authentication measures that have been enabled.
For a long time, sophisticated APT groups have used reverse proxies to circumvent MFA safeguards on target accounts, some using their own bespoke tools and others utilizing more easily deployable kits like Modlishka, Necrobrowser, and Evilginx2.
EvilProxy makes it way too easy for hackers to steal user data
The difference between these phishing frameworks and EvilProxy is that the latter is much easier to set up, with thorough instructional videos and tutorials, a user-friendly graphical interface, and a large collection of cloned phishing sites for famous online services.
According to Resecurity, EvilProxy provides an easy-to-use GUI where threat actors may set up and manage phishing campaigns and all the elements that go with them. For $150 for ten days, $250 for twenty days, or $400 for a month-long campaign, the business claims to steal usernames, passwords, and session cookies. Attacks against Google accounts are more expensive, costing $250/450/600.
In a video, Resecurity shows how an assault on a Google account would proceed using EvilProxy. While the service is frequently pushed on numerous clearnet and dark web hacking forums, the clients are vetted, so some prospective purchases are likely to be refused.
According to Resecurity, payment for the service is made on Telegram individually. After making a deposit, the customer gains access to the portal housed on the onion network (TOR). The platform’s testing by Resecurity verified that EvilProxy also provides VM, anti-analysis, and anti-bot protection to filter out invalid or unwanted visitors on the platform’s phishing sites.
Alleged cybersecurity issues of Twitter is causing a headache for the firm
Resecurity explains in the report, “The bad actors are using multiple techniques and approaches to recognize victims and protect the phishing-kit code from being detected. Like fraud prevention and cyber threat intelligence (CTI) solutions, they aggregate data about known VPN services, Proxies, TOR exit nodes and other hosts which may be used for IP reputation analysis (of potential victims).”

As MFA use grows, more threat actors turn to reverse-proxy techniques, and the development of a platform that automates everything for criminals and is bad news for security experts and network administrators.
The phishing email detection tool can help users avoid cyber-attacks
For the time being, the only way to address this issue is to use client-side TLS fingerprinting to detect and filter out man-in-the-middle requests. However, the industry’s implementation status is out of pace with the advances.
As a result, services like EvilProxy effectively bridge the skill gap and provide low-tier threat actors with a low-cost option to steal important accounts.






